Technology has made running a business easier, but there are hidden costs that must be considered. New computers are a single purchase, but energy consumption, bandwidth usage, and part replacement/repair are all associated costs. Obviously, you can plan your budget accordingly for these. But what happens when a third party tricks you into shouldering the financial burden of their exploits? Cryptojacking is one such scheme that could be secretly costing your business money.
Cryptojacking is the unauthorized use of your company’s computers to mine cryptocurrency and there are several ways that a hacker can pull this off.

In the beginning, cryptojacking required the victim to unknowingly download software that would run in the background. Hackers used techniques similar to a phishing scam; they would send legitimate-looking emails and trick users into clicking on harmful links that install malicious software. This secret software then uses the target’s CPU to run complex mathematical tasks to “mine” cryptocurrency.
Currently, the most ubiquitous form of cryptojacking is through your internet browser. Browser mining involves a site, either knowingly or unknowingly, employing a Javascript which runs through your browser when visiting said site. Hackers can exploit unwitting websites (sometimes using infected ads) to do this, but some sites do this intentionally. CoinHive is one such program and it has been used by some companies as a way to earn revenue without involving traditional advertisements. This is, of course, highly controversial.
Mining cryptocurrency is purpose-built to require massive amounts of computer power to regulate the overall pool of a particular currency or coin. Hackers can aggregate or “hash” computer power from hundreds of unknowing victims, effectively forcing them to foot the bill for their endeavors. This may seem relatively harmless compared to schemes like WannaCry, which held your data hostage and only relinquished its grip upon receiving a payment or ransom. Cryptojacking, however, is not without its own harmful consequences.
Most of these programs run in the background and are undetectable by most traditional means. They often wait until the user is away before starting up and close down as soon as they return. This makes it incredibly difficult to even know when you’re a target of such an attack. The real damage is only realized when you open your electricity bill that month or are forced to start replacing overworked computer components. While a few hours of mining won’t break your bank, that process repeated every day on dozens of computers through the course of a month starts to add up.

So what can you do to prevent these guys from turning your machines into their personal army of miners? First and foremost, it is important to educate your employees about the dangers of phishing tactics. The best defense for these sorts of attacks is always knowledge. Take a look at our phishing blog for a more in-depth look at that topic.
There are also a variety of different browser extensions you can have installed that will detect and block sneaky scripts. “No Coin” and “Minerblock” are two such extensions available.
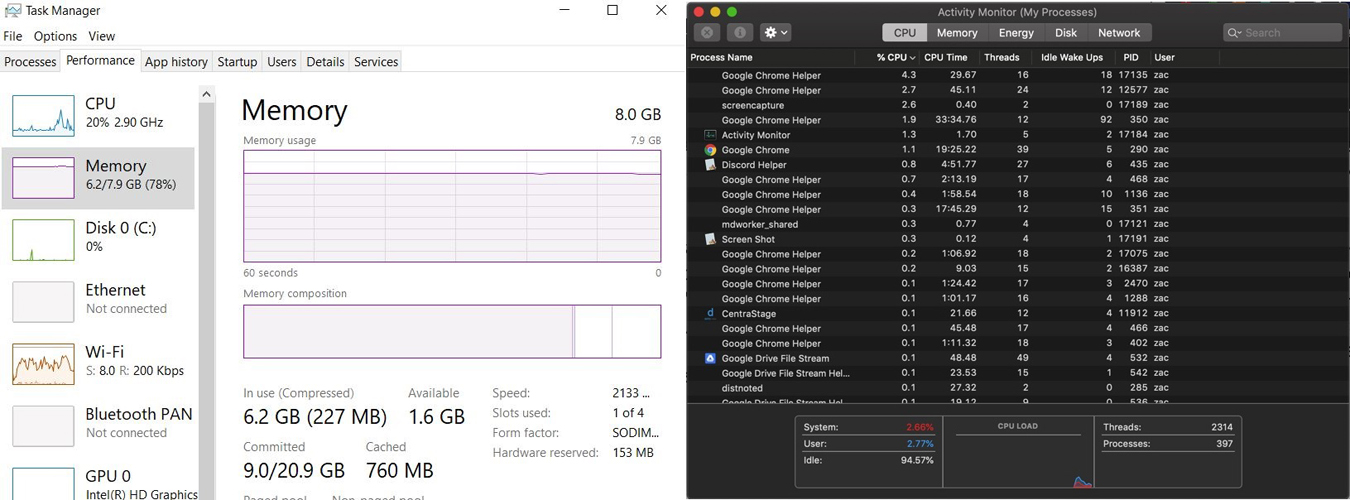
If you suspect that a particular site is running a mining script, you can always check your computer’s CPU performance to see if it is working harder than normal. If your business uses Windows, you can check performance in the Task Manager (press CTRL + ALT + DELETE, click “Task Manager” and then navigate to the “Performance” tab). If you use Mac, the Activity Monitor performs the same function (go to your “Applications” folder, then “Utilities” folder where you’ll find the icon).
If Java isn’t central to your daily tasks, consider disabling Javascript on your internet browser. If you’re uncertain, it’s always best to ask your IT professional before doing this. This ensures that any site running mining scripts won’t be able to hijack your resources to do so.
Finally, you can offer your business the highest form of protection by working with a Managed IT Service Provider (like Pretect!). We use the latest monitoring software to keep an eye on your network’s performance. If a machine has a sudden spike in the resources used, a flag is immediately raised. This means you can stop these exploitative processes before they have a chance to cost you money.
We hope you found this blog helpful! If you have any questions or want to learn more about what Pretect can do for your business, visit our site!

